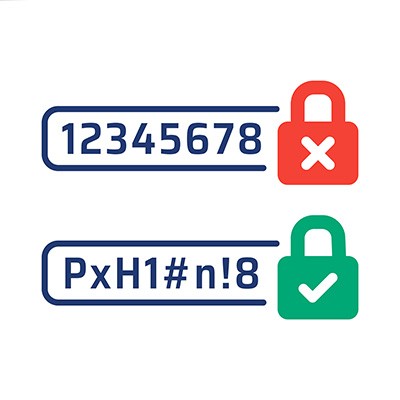
You’ve probably heard a lot of password advice over the past decade, but how much of it is actually good advice that you should listen to? These days, with advanced automated threats able to crack incredibly complex passwords with ease, you can’t be too careful. You might even need to take a different approach entirely… which brings us to the OG password advice: just make it longer.
About CoreTech
CoreTech has been serving the Kentucky area since 2006, providing IT Support such as technical helpdesk support, computer support and consulting to small and medium-sized businesses. Our experience has allowed us to build and develop the infrastructure needed to keep our prices affordable and our clients up and running.
Recent News
Contact Us
1711 Destiny Lane Suite 116
Bowling Green, Kentucky 42104
Mon to Fri 8:00am to 5:00pm
Nashville Managed IT
Louisville and Lexington Managed IT
Bowling Green Managed IT
Clarksville Managed IT